Categories
Recent Stories
Topological Qubits Explained: The Science Behind Majorana 1
Mar 3, 2025 Information hub
Dive into topological qubits, the stable science behind Microsoft’s Majorana 1. Learn how they work and why they’re a quantum breakthrough.

Quantum Computing History: Evolution to Microsoft Majorana 1
Feb 28, 2025 Information hub
Explore quantum computing history, from early theories to Microsoft’s Majorana 1. Learn how this tech grew into a game-changer over decades.
Quantum Chip: The Heart of Next-Gen Computing
Feb 28, 2025 Information hub
Curious about a quantum chip? Learn what it is, how it works, and why it could revolutionize computing with speed and power.
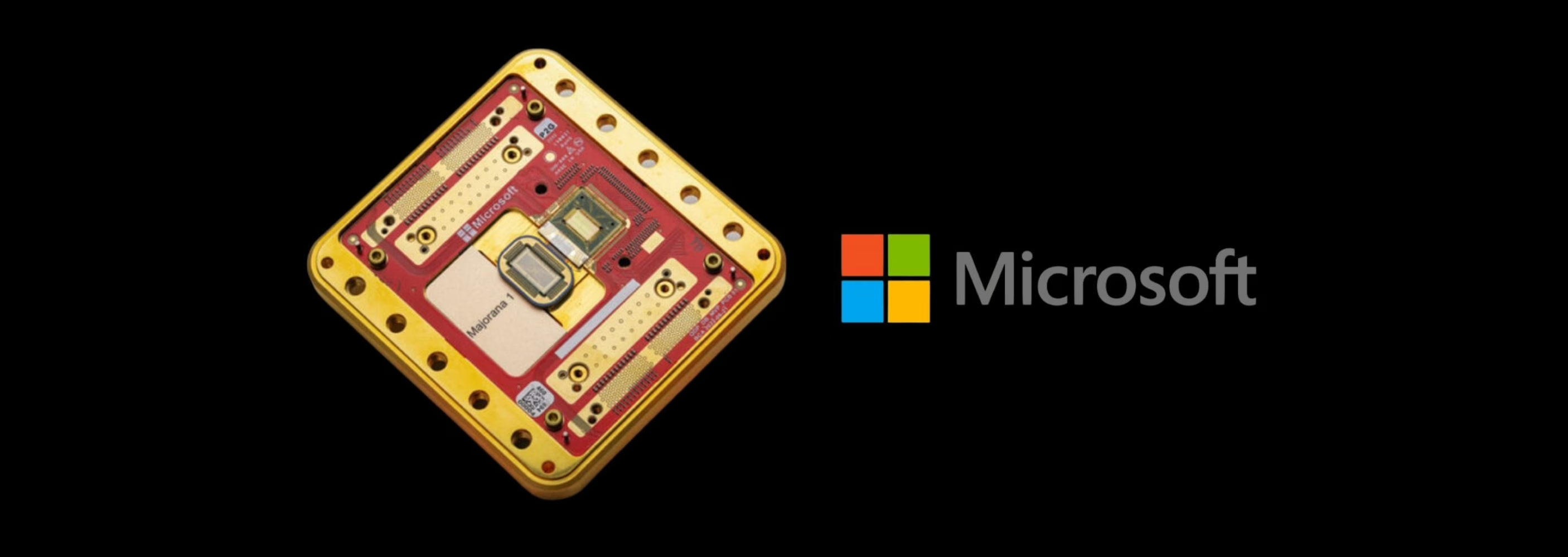
Microsoft Majorana 1: The Next Big Thing in Quantum Tech
Feb 26, 2025 Information hub
Meet Microsoft Majorana 1, a new quantum chip that’s stable and strong, ready to change tech in 2025.
Microsoft Quantum Chip: Quantum Computing in 2025
Feb 26, 2025 Information hub
Discover the Microsoft quantum chip, Majorana 1, and its topological qubits revolutionizing quantum computing in 2025.
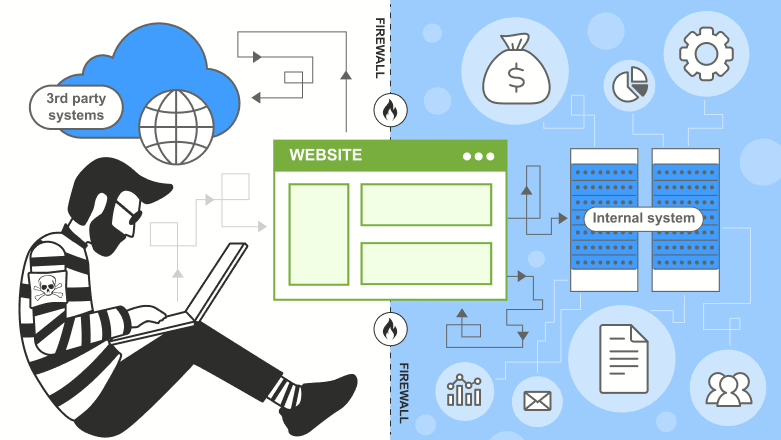
AI Cyber Security: UK’s 2025 Code of Practice Unveiled
Feb 25, 2025 Information hub
Discover the UK’s 2025 AI cyber security Code of Practice. Explore 13 principles, real-world applications, and recent threats in this guide.
AI Cybersecurity: Securing AI Systems in 2025
Feb 25, 2025 Information hub
Explore AI cybersecurity in 2025 with the guide to secure AI systems. Learn key principles, real-world scenarios, and recent threats.
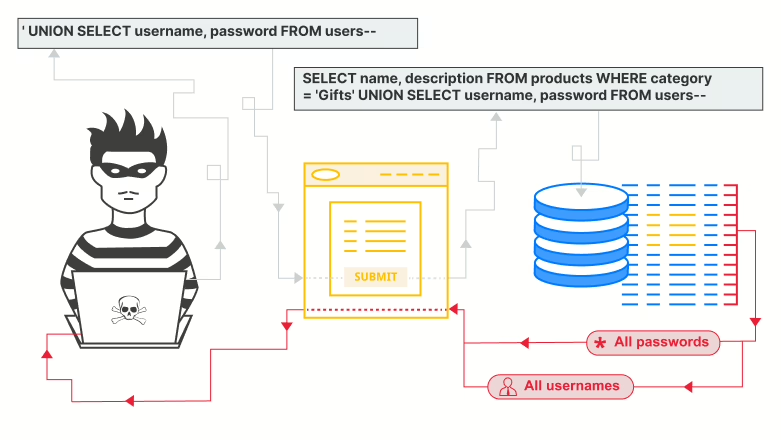
Vector and Embedding Security: Protecting LLMs from Threats
Feb 7, 2025 Information hub
Learn about Vector and Embedding Security, its risks, challenges, and solutions to safeguard LLMs from adversarial attacks and data breaches.