Categories
Recent Stories
A Quick Note For AWS Penetration Testing: Securing Your Cloud Infrastructure
Nov 26, 2024 Information hub
Discover AWS penetration testing and its importance in identifying vulnerabilities in cloud environments. Learn methods, tools, and best practices to ensure data and workload security.
Comparing Vulnerability Management Frameworks: CISA, NIST & SANS
Nov 26, 2024 Information hub
Explore vulnerability management frameworks like CISA, NIST, and SANS. Learn tools and strategies to identify, assess, and fix vulnerabilities effectively.
Vulnerability Assessment Types & Methodologies Explained
Nov 22, 2024 Information hub
Explore various vulnerability assessment types & methodologies to safeguard your network, systems, and applications from potential security threats.

What Is Vulnerability Assessment and How Is It Conducted?
Nov 22, 2024 Information hub
Discover the importance of vulnerability assessments in identifying security risks and protecting your systems from potential attacks. Learn how it's done and why it matters.
Vulnerability Tracking Using OCRC: A Structured Framework for Effective Penetration Testing
Nov 21, 2024 Information hub
Discover how the OCRC framework enhances vulnerability tracking in penetration testing with clear stages—Open, Confirmed, Resolved, and Closed.

Cloud Data Security Best Practices: Comprehensive Guide
Nov 19, 2024 Information hub
Discover cloud data security best practices to secure your business's sensitive information against unauthorized access and cyber threats.
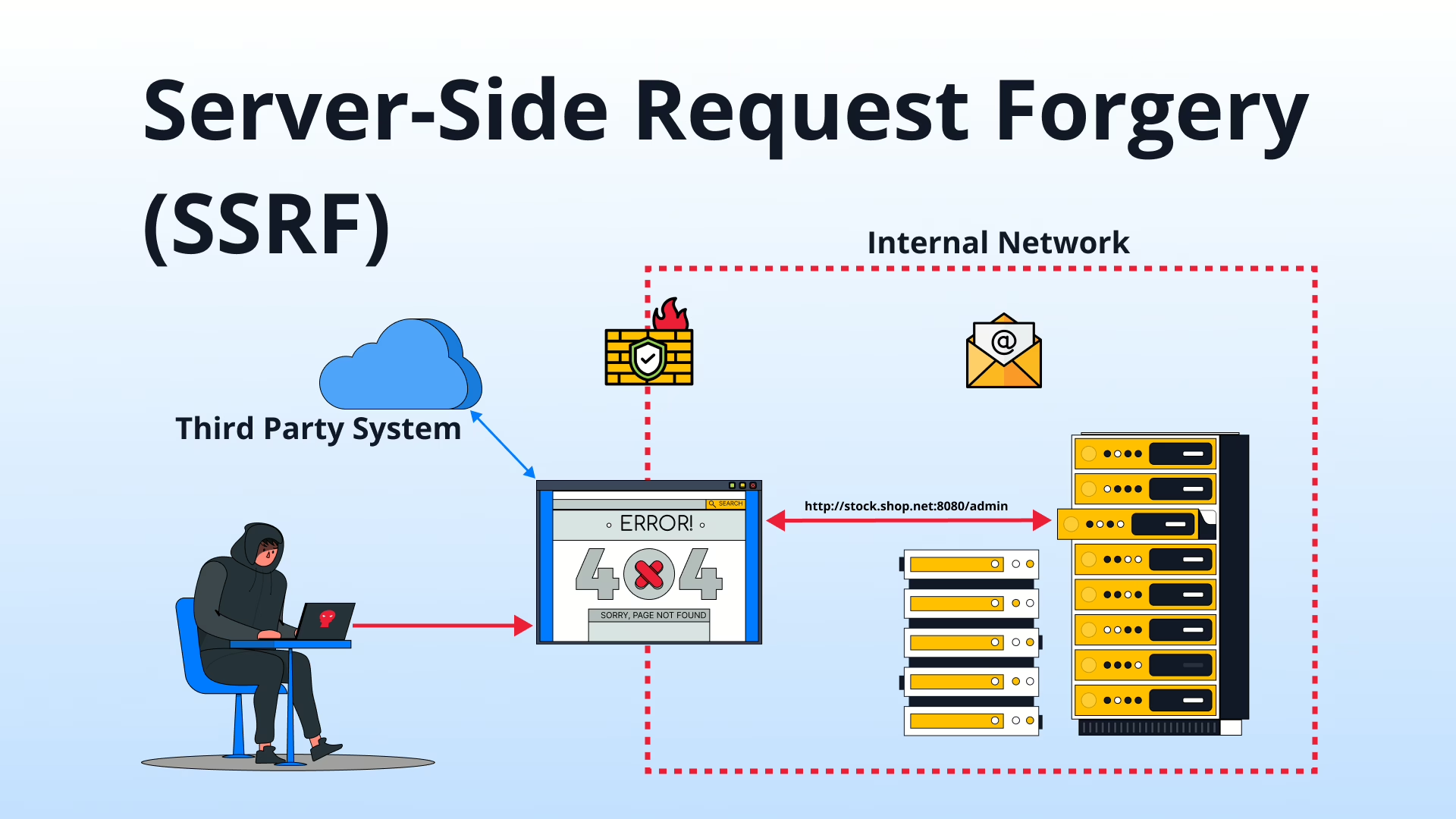
Server-Side Request Forgery (SSRF): Threats and Mitigation
Nov 15, 2024 Technical Write ups
Server-Side Request Forgery (SSRF) is a critical vulnerability that attackers exploit to access sensitive data. Discover its risks, real-world examples, and effective mitigation strategies.

ASR Rules: Key to Blocking Cyber Threats & Enhancing Security
Nov 11, 2024 Information hub
Discover how ASR rules can protect your organization by blocking risky activities, preventing credential theft, and securing endpoints for robust digital defenses.
