Categories
Recent Stories
Viruses vs. Worms vs. Trojan Horses: A Detailed Guide With Prevention Tips
Oct 11, 2024
Explore the distinctions between viruses, worms, and Trojan horses in this guide. Understand how each operates, with examples, and learn essential cybersecurity tips for staying protected.
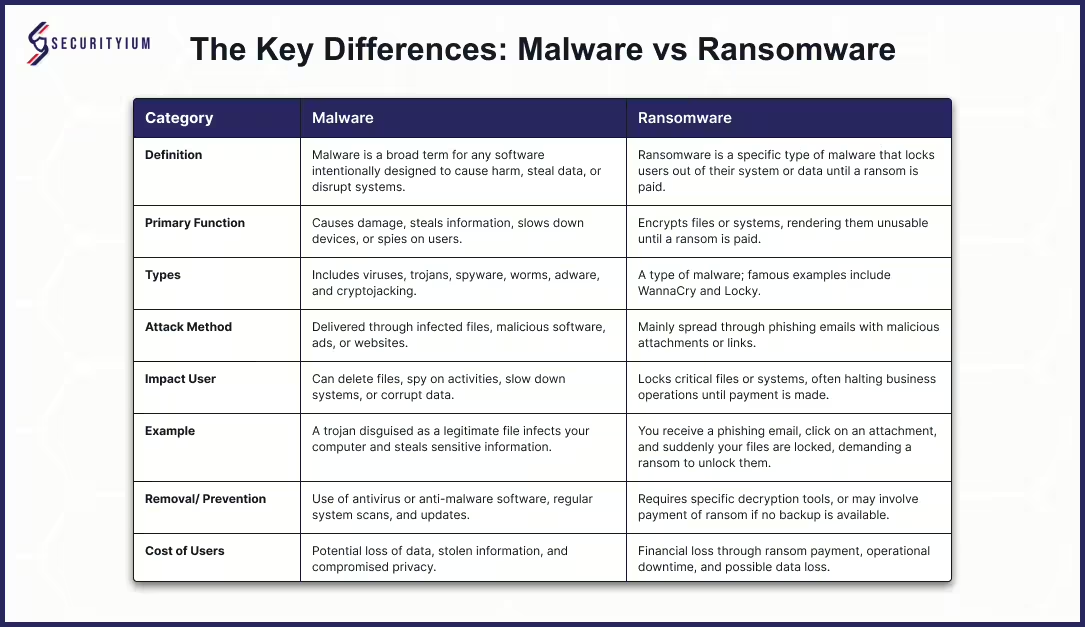
Malware vs Ransomware: Unmasking the Key Differences
Oct 8, 2024 Information hub
Learn the differences between malware and ransomware, their attack methods, and effective prevention strategies to safeguard your data.
A Vulnerability in reNgine: CVE-2024-43381
Aug 26, 2024 Bug hunting
Learn about CVE-2024-43381, a Stored XSS vulnerability in reNgine. This article covers how the flaw works, its potential risks, and key strategies to mitigate the threat.
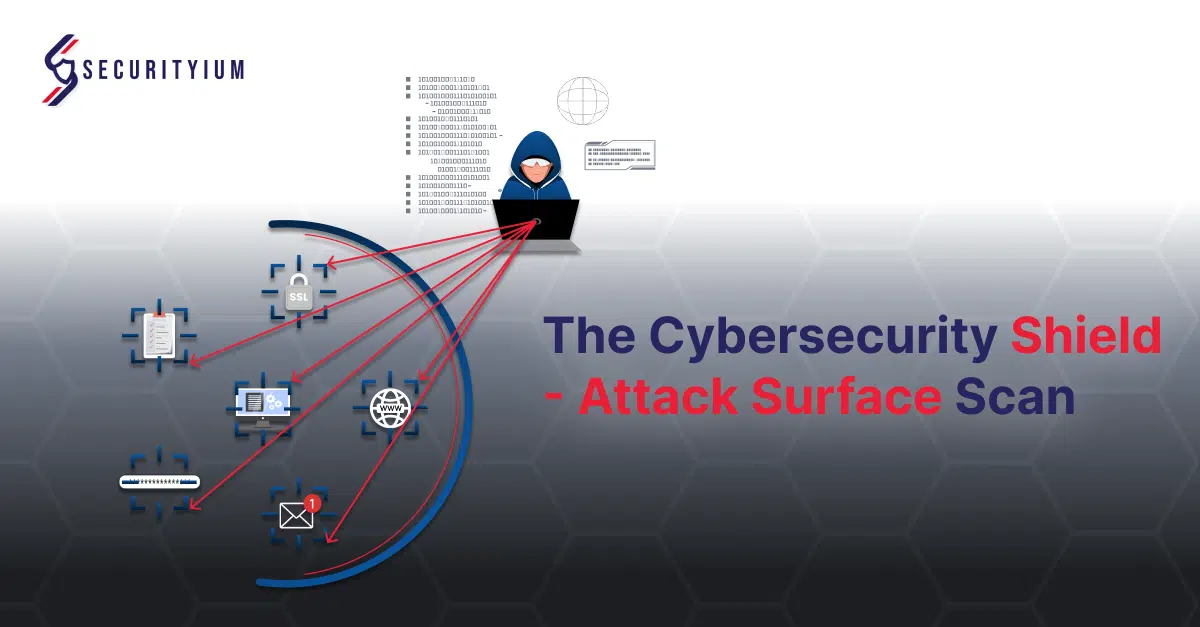
The Cybersecurity Shield – Attack Surface Scan
Aug 23, 2024 Information hub
Enhance your cybersecurity with attack surface scanning. Discover vulnerabilities, safeguard digital assets, and ensure compliance. Explore our blogs for such proactive strategies.
Understanding Incremental Penetration Testing
Aug 9, 2024 Information hub
An Incremental Penetration Test is an approach of security testing that focuses specifically on evaluating the security of new or modified features in an application since the last full penetration test.
Supply Chain Management in Cybersecurity
Jul 4, 2024 Information hub
Protect your business from supply chain attacks with Securityium's comprehensive strategies and insights on mitigating cybersecurity risks effectively.
Vendor Impersonation Threat in IT Security
Jun 27, 2024 Information hub
Protect your business from phishing attacks with Securityium's insights on preventing cyber threats through robust IT security measures and training.
Preventing Phishing-Induced Data Breach
Jun 20, 2024 Information hub
Prevent data breaches with Securityium's insights on phishing risks, breach causes at Dropbox, and proactive cybersecurity measures.
